A new report in Wired magazine details how Iran has been target of a "Shadow Brokers-style" hack campaign which seeks to expose methods, names, and activities behind an elite cyber-espionage team linked to Iran's Ministry of Intelligence.
The Shadow Brokers leaks from 2016 famously targeted the National Security Agency, dumping tools used by the agency online, and later resulted some of the most devastating cyberattacks in history such as the NotPetya and Wannacry attacks, which devastated networks all over the world. Now it appears it's Iran's turn to be targeted by a powerful mystery group doxing Iran's foremost hacking team.

The leaks have been ongoing for the past month, as Wired reports:
Since March 25, a Telegram channel called Read My Lips or Lab Dookhtegan—which translates from Farsi as "sewn lips"—has been systematically spilling the secrets of a hacker group known as APT34 or OilRig, which researchers have long believed to be working in service of the Iranian government. So far, the leaker or leakers have published a collection of the hackers' tools, evidence of their intrusion points for 66 victim organizations across the world, the IP addresses of servers used by Iranian intelligence, and even the identities and photographs of alleged hackers working with the OilRig group.
The motive appears political in nature, given that along with the Iranian hackers' code being dumped online, the mystery agent behind the leaks posted the following message to Telegram in late March: "We are exposing here the cyber tools (APT34 / OILRIG) that the ruthless Iranian Ministry of Intelligence has been using against Iran's neighboring countries, including names of the cruel managers, and information about the activities and the goals of these cyber-attacks."
And further, the initial message ended with, "We hope that other Iranian citizens will act for exposing this regime's real ugly face!"
OilRig has long been seen by researchers as an arm of the the Iranian Ministry of Intelligence, active for several years against a number of Middle East and international companies and organizations, and often often starts by executing intrusions against organizations in the supply chain of a larger target.
Whoever is dumping Iran’s cyber-tools is deliberately excising core elements of the code so others can’t easily repurpose them for nefarious reasons (unlike The Shadow Brokers) ��
https://t.co/K1Ie3gxR4p
— Aki Peritz (@AkiPeritz)
April 19, 2019
As of Thursday morning, the Read My Lips leakers continued to post names, photos, and even contact details of alleged OilRig members to Telegram, though WIRED couldn't confirm that any of the identified men were actually connected to the Iranian hacker group. "From now on, we will expose every few days the personal information of one of the cursed staff and secret information from the vicious Ministry of Intelligence so to destroy this betraying ministry," a message posted by the leakers on Thursday read.
A private cybersecurity research firm cited in the report has confirmed that at least some of the hacking tools released in the mystery attacks and code dumps match OilRig's hacking tools, and have identified victim companies that have been known to have been targeted by Iranian intelligence in the past.
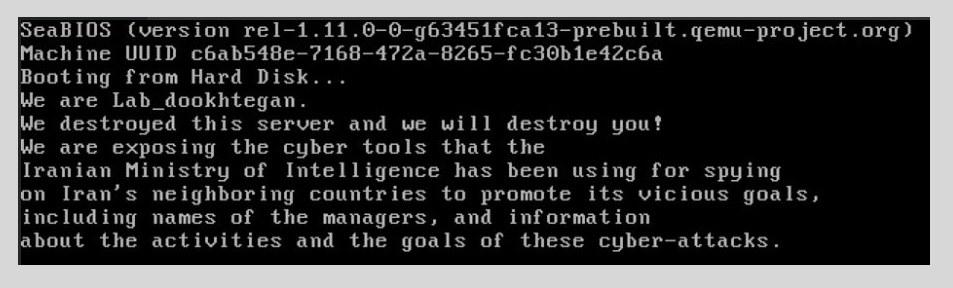
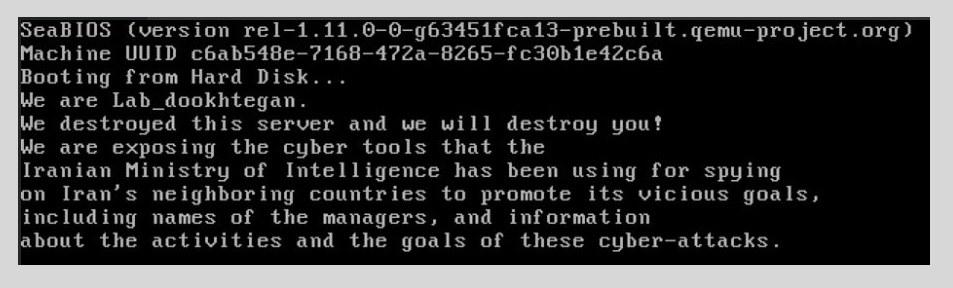
It further appears a major and "embarrassing" setback for Iranian cyberintelligence, given further that "the Read My Lips leaker also claims to have wiped the contents of Iranian intelligence servers and posted screenshots of the message it says it left behind, like the one shown below," according to the report.
Screenshot of message left by mystery hackers targeting Iranian intelligence, via Wired:
"We have more secret information about the crimes of the Iranian Ministry of Intelligence and its managers," a message from the mystery agent posted last week promises. "We are determined to continue to expose them. Follow us and share!"
A number of online commentators have speculated that it could be US or Israeli intelligence conducting the current cyberattacks on the Iranian group, while under the guise of a Shadow Brokers-style independent hacker group.
https://www.zerohedge.com/news/2019-...ack-and-doxing





 Reply With Quote
Reply With Quote












Connect With Us